Mobile banking security. So far it is better than on a desktop
Access to the serviceóBanking with mobile devices is becoming more and more common and certainly the number of usersóIn the coming years, the number of such solutions will grow rapidly. I have good news for those whoówho carry out banking operations using a smartphoneóin and tabletów – so far, this is a much safer way to connect to the bank than using a PC. Mobile banking applications are very safe, and so far we have not found any malicious code in our laboratories thatóIt is advisable to take a break and leave the locked room for a few minutes.
The only problem is that there are many versions of banking applications. There are often private applications, whichóre served their twórcom to enter „onóyou” to their bank account. For obvious reasons such unofficial applications should be avoided as much as possible. Another problem may be that there are multiple language versions of the same banking app, whichóre adapted to the needs of local marketsów. The multitude of such variantsóThe new system has arrived in Europe faster than anyone expected, with restrictions on travelów. In order to avoid misunderstandings it is best to check on the bank’s website which application is dedicated to the country from which the user is connectedóecause. This should definitely make things easier. It is worth mentioning hereóccess to the search engine on your pc.
Mobile phonesóMobile phones can of course be used toób to break bank account security, but so far it has always occurred in the context of operations executed on PCs. Such an example is the Trojan Perkele wreaking havoc about a year ago.
Perkele’s mechanism took advantage of the fact that many banksóIn order to confirm operations the bank uses mobile phonesóThe Trojans are used to send transaction confirmation data, i.e. mobile Transaction Authentication Number (mTAN) tokens. Once installed, Perkele trojan monitored incoming SMS messages and scanned them for mTAN number.
Of course, this trojan was only one part of the whole operation. It complemented the computer component that infects websites by injecting code. When a user visited infected banking website, he was asked to enter a numberóin the phone in order to receive „security application” from the bank. The user then received an SMS message with a link to download the application. After installing PerkeSecuApp. A displays or performs fake operations, and silently intercepts SMS messages in the background.

Beware of phishing in mobile
Threats related to mobile internet browsers in the context of online banking are connected mainly with phishing, This is more a social engineering method than an IT method. The effectiveness of phishing is still high, despite the fact that for many years there have been repeated appeals, and users are constantly informed about what kind of messages are definitely not sent to them by auction services or banks.
In the case of mobile devices, this effectiveness is due to a very prosaic issue, which is the size of the phone screen, whichóra definitely limits the readability of displayed pages. In this case, it is much easier to mistakenly push a link that leads the user to a place where they would rather not go.
The more data, the more threats
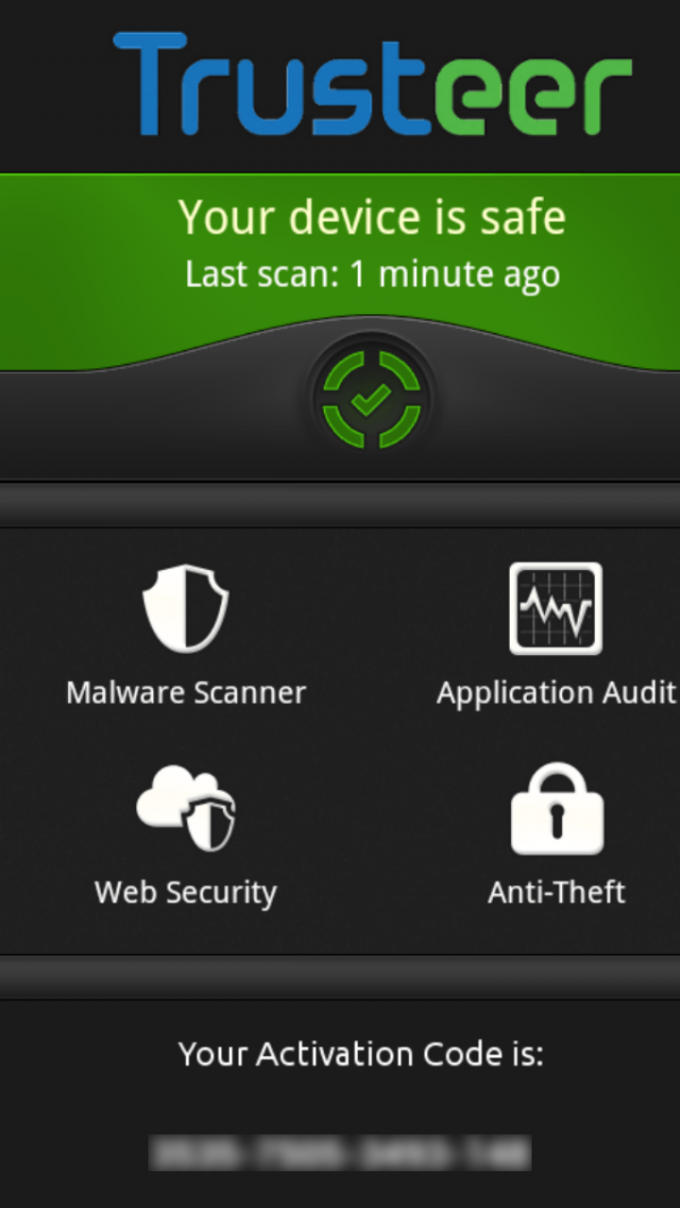
Of course, mobile security is not only about online banking. In fact, on our mobile devices we have accumulated a lot of information and fileóin whichówe rather do not want to share with anyone, and certainly do not want to lose them. Therefore, you should equip your tablet and smartphone with appropriate antivirus protection to block potential malware. This is a particularólncreasingly important now with the number of threats to mobile platforms, and in particularóThe number of applications for Android is growing at an almost exponential rate. According to our Laboratory’s data, as many as 97 percent of. malicious programsóIn 2013, more than three times as many new malware families were created’than in the previous year. Surely this trend will continue as the number of mobile devices in our possession increases. What’s more, cybercriminals will probably want to exploit vulnerabilities in software thatóThey have their counterparts in PC versions. Such an example is the flash player in web browsers, and its vulnerability to róThe problem of malicious attacks is a major concern for many network administrators.
The last thing, on whichóThe one thing to be very careful of is to control Bluetooth module and connecting to public Wi-Fi networks. As a precaution, it’s always a good idea to turn off your modem and Bluetooth when you’re not using them. It’s already the case that marketers are using Wi-Fi MAC address tracking, and since they’re doing it, it’s probably wkrótce the method will be used by persons with bad intentions.
In the case of public Wi-Fi networks, it is important to pay attention to the security of the networkóThere is one more issue that should be noted – otóthat they are often unsecured, so it is very easy to trace the connections of logged on usersów. This makes it possible for hackers to access sensitive information, such as mail or banking service credentials, among others, as long as they are opened in a web browser, of course.
A good solution in this case is to installing a VPN, that is, a virtual private network that encrypts the connection making it impossible to intercept data. In the case of F-Secure, such a solution is Freedome, whichóry not only encrypts the connection, but also scans the downloaded content in the cloud for virusesów. Such a solution enables free use in public Wi-Fi networks all over the world.
Mobile devices are increasingly vulnerable to róattacks of various types. History teaches that as the popularity of a given platform increases, more and more malware is created for it. This is the fate of Windows and it will certainly happen to Android. Detailsólno that Google’s system is more open than iOS and Windows Phone. We should be very vigilant and not make it easy for those whoówho lurk for our information and money.
Author
 Sean Sullivan, a consultant for. F-Secure security.
Sean Sullivan, a consultant for. F-Secure security.